TCS NQT Menu
- Placement Papers
- What is TCS NQT?
- How To Apply
- Foundation Section
- Aptitude Questions
- English Verbal
- Reasoning Ability
- Advanced Section
- Advanced Quantitative Ability
- Advanced Reasoning Ability
- Advanced Coding
- Coding Questions
- Syllabus
- Eligibility Criteria
- Recruitment Process
- Registration Process
- TCS NQT Salary
- How to prepare for TCS NQT?
- Interview Questions
- Hiring Process
PREPINSTA PRIME
TCS Interview Questions and Answers
TCS Interview Questions and Answers 2025
Read the frequently asked questions from the TCS interview as well as some additional details on the interview rounds and common topics on which questions are asked.
Page Highlights:
- TCS Interview Rounds
- TCS Interview Questions and Answers

TCS Interview Rounds
TCS conducts interview rounds in two phases after the online test, and they are:
- Technical Round/MR Round
- HR Round
Most Asked Topics in TCS Interview:-
- Programming Questions ( C, JAVA, Python, C++)
- OOPS concepts
- Computer Network
- DBMS
- DSA
- Operating Systems
TCS nowadays also asks questions about the latest technologies such as Artificial Intelligence, Blockchain, IoT, Machine Learning, Deep Learning, etc.
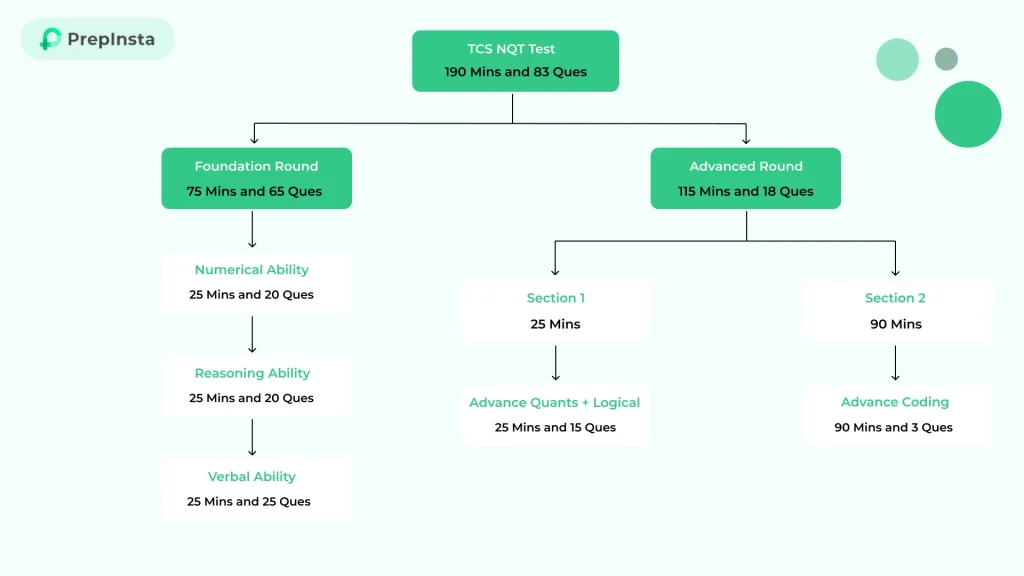
TCS Online Test Pattern
TCS Interview Questions and Answers
Getting ready for a TCS interview? This guide has you covered! Here’s what you’ll find inside:
Most commonly asked TCS interview questions
Smart strategies to frame impressive answers
Tips for both freshers and experienced candidates
Expert insights into technical, HR, and behavioral rounds
TCS Technical Interview Questions:
Question 1: What is IPsec?
Answer:
IP Security (IPSec) is a group of Internet Engineering Task Force (IETF) standard protocols that provide data integrity, confidentiality, and authentication between two communication points over an IP network. Additionally, it describes the encryption, decryption, and authentication processes for packets. It outlines the protocols for secure key management and exchange.
Question 2:- What are the differences between classes and interfaces?
| Class | Interface |
|---|---|
| A class can be created by making its object. | An interface can’t be created from scratch. |
| When defining a class, the class keyword is used. | When defining an interface, the interface keyword is used. |
| Access specifiers like public, protected, and private may apply to class members. | Accessing specifics contained within an interface member will be useless. |
| The actions that can be taken on the fields declared in the class are defined for the methods inside the class. | The ways in an interface are completely abstract, and it lacks assertion in certain areas. |
| A constructor can be defined inside a class to declare the fields inside the class. | The absence of initializable fields prevents the definition of a conductor for the interface. |
Question 3: What are the components of IPsec?
Answer:
Encapsulating Security Payload (ESP): ESP offers all of the following services: data integrity, encryption, authentication, and anti-replay. Furthermore, payload authentication is supported.
Authentication Header(AH): This header does not provide encryption, but it does support data integrity, authentication, and anti-replay. Anti-replay security prevents unauthorized packet transmission. It does not guarantee data privacy.
IKE (Internet Key Exchange): It is a network security protocol that enables two devices to connect over a Security Association and exchange encryption keys on-the-fly (SA). IKE (Internet Key Exchange) acts as an open framework for implementing widely used algorithms like SHA and MD5. It also protects the content of messages.
Questions 4: Define NAT.
Answer:
The term Network Address Translation is abbreviated as NAT (Network Address Translation). Rerouting traffic over a traffic routing device requires changing the IP headers of packets in order to remap one IP address space to another.
Question 5: What Is Tensorflow, and What Is It Used For?
Answer:
A software library called TensorFlow was created as an open-source resource for machine learning and neural network research by the Google Brain Team. Data-flow programming is done using it. Natural language processing and speech recognition are only two of the AI technologies that TensorFlow makes much simpler to incorporate into the software.
Question 6: Define SLIP.
Answer:
Serial Line Internet Protocol (SLIP) is a TCP/IP-based fundamental protocol for communication through serial ports and routers. They enable previously configured computers for direct communication to communicate with one another.
Question 7: What Is Machine Learning, and How Does It Relate to AI?
Answer:
Machine learning is a subset of artificial intelligence. The concept is that machines will “learn” and improve at activities over time rather than requiring humans to constantly input settings. Machine learning is a practical application of artificial intelligence.
Question 8: Explain memory leak in C++. How can you avoid it?
Answer:
Memory leakage occurs in C++ when programmers allocate memory dynamically using the new keyword or malloc()/calloc() and then fail to deallocate it using the delete() or delete[] operators or the free() function. One of the most common causes of memory leakage in C++ is the inappropriate usage of the delete operator. To free an array of data values, use the delete [] operator, but to remove a single allocated memory area, use the delete operator.
Avoiding memory leak:
- Use smart pointers instead of manually managing memory whenever possible.
- std::string should be used instead of char *. All memory management is done internally, which makes it swift and efficient.
- You should never use a raw pointer unless you are communicating with an older library.
- The simplest way to avoid memory leaks in C++ is to have a few new/delete calls at the program level as feasible — preferably NONE.
- To allocate and deallocate memory, place all code between the new and delete keywords.
Questions 9:What do you understand by a command-line argument in C?
Answer:
C uses command-line arguments to retrieve parameters from the command prompt. In C, the main function accepts three arguments. They are as follows:
- Argument counter
- Argument vector
- Environment vector
Questions 10: Write a program for Fibonacci using C++.
// Write a program to print fibonacci series in C++ #includeusing namespace std; int main() { int num = 15; int a = 0, b = 1; // Here we are printing 0th and 1st terms cout << a << ", " << b << ", "; int nextTerm; // printing the rest of the terms here for(int i = 2; i < num; i++){ nextTerm = a + b; a = b; b = nextTerm; cout << nextTerm << ", "; } return 0; }
Question 11: Define Java Development Kit (JDK), Java Runtime Environment (JRE), and Java Virtual Machine (JVM) briefly.
Answer:
JAVA Development Kit: JDK is short for Java Development Kit. It is a setting for the development of Java applications and applets. It actually exists. Developer tools are also included, along with JRE. JDK is an implementation of any of the following Java Platforms made by Oracle Corporation:
- Java Platform Standard Edition
- Java Platform Enterprise Edition
- Java Platform Micro Edition
JAVA Runtime Environment: The term Java Runtime Environment (JRE) refers to the Java Runtime Environment. It is the Java Virtual Machine implementation. The Java Runtime Environment (JRE) is a set of software tools used to develop Java applications. It is in charge of generating the runtime environment. It is the Java Virtual Machine implementation. It truly exists. It consists of a collection of libraries and other files that the JVM uses during execution.
JAVA Virtual Machine: JVM is an abstract machine that provides a runtime environment for Java byte-code execution. It is a specification that describes the operation of the Java Virtual Machine. Oracle and other corporations have aided in its adoption. The program that implements it is known as JRE.
JVMs are available for a wide range of hardware and software systems (so JVM is platform-dependent). When the Java class is executed, a runtime instance is produced. The JVM is split into three sections:
- Specification
- Implementation
- Instance.
Question 12: What is metadata? What is its purpose?
Answer:
Metadata is information about the data stored in an HTML document. This is accomplished by the use of thetag. Browsers, web services, and search engines can employ metadata to store information such as keywords, page descriptions, and the latest changed dates
Question 13: Write a program to print the sum of digits in JAVA.
public class Main
{
public static void main (String[]args)
{
int num = 12345, sum = 0;
//loop to find sum of digits
while(num!=0){
sum += num % 10;
num = num / 10;
}
//output
System.out.println ("Sum of digits : " + sum);
}
}
Question 14: What is slice splicing in software testing? What are its two types?
Answer:
Slicing, also known as program slicing, is a software testing approach that uses a slice or a collection of program statements to test specific test cases or test conditions that may have an impact on a value at a specific point of interest.
There are two forms of slicing:
Static Slicing:
All of the statements in a program’s static slice have the potential to alter a variable’s value at any time throughout any execution of the program. Static slices are typically larger. It takes into account every conceivable program execution.
Dynamic slicing:
A dynamic slice of a program consists of all the statements that truly affect a variable’s value at any given time for a particular program run. Dynamic slices are typically thinner. Only considers the execution of a specific program.
Question 15: What is a style sheet?
Answer:
It is a file that details how an HTML document or web page should be laid together. For instance, a stylesheet controls everything from fonts and sizes to margins and spacing for text. CSS is the most widely used format (Cascading style sheets).
Question 16: How do you differentiate between AWT and Swing in Java.
| AWT | Swing |
|---|---|
| A Java API for building graphical user interfaces is called Java AWT. | Java Foundation Classes, which are used to create a range of programs, include Swing. |
| Java AWT components are made up of heavyweight. | Java Swing is made up of lightweight components. |
| AWT takes longer to execute than Swing does. Comparatively speaking, AWT components are less potent. | The swing takes less time to execute than AWT does. Comparatively speaking, swing components are more potent. |
| The Java AWT components are depending on the platform. | Regardless of the platform, Java Swing components are platform-independent. |
| AWT doesn’t support the MVC pattern. | MVC is supported by Swing. |
Question 17: What do you mean by subnet mask?
Answer:
A Subnet Mask is a number that indicates the range of IP addresses that can be utilized within a network. They are given subnets or subnetworks. These subnetworks are made up of LANs that are connected to the internet.
This Subnet mask is a 32-bit variable that splits the IP address into two parts:
- The network address
- The host address.
Question 18: What do you understand by piggybacking?
Answer:
Piggybacking typically has no harmful intent, just the desire to acquire free network access, but it can slow down data transfer for authorized users of the network.
Question 19: What do you mean by the RSA algorithm?
Answer:
Data transfer security is provided by the RSA cryptography technique. This method encrypts data using a public key, while the decryption key is kept private or hidden. The encryption key, which is then made public along with an auxiliary value, is created using two enormous prime integers. Anyone can encrypt data using this public key, but only someone who is familiar with prime numbers may decrypt it. But because this method is thought to be sluggish, it is not generally employed to encrypt data.
Question 20: What are the various SDLC methodologies?
Answer:
There are 6 models –
- The waterfall model
- V-shaped model
- Iterative model
- Spiral model
- Big bang model
- Agile model
Also Check:
TCS HR Interview Questions
Question 1: Tell me about yourself.
Answer:
I’m Harshal, I was born in Jammu, and I’m currently studying a B.E. in Computer Engineering at the XYZ Institute of Technology. As of the seventh semester, my overall grade point average is 80%. I completed my secondary education at ABC School with an 80 percent grade point average. I have also worked on small projects and represented my college at various university levels. My interests include playing cricket and drawing. In high school and college. My ultimate goal is to work at a company that I enjoy, and yours can give me that chance.
That’s all about myself.
Read more at: Tell me about yourself.
Question 2: What are your strengths and weaknesses?
Answer:
My strengths are, that I have an optimistic outlook, I’m a creative learner, and I’m dedicated to my work. Procrastination is one of my weaknesses.
Read more at: What are your strengths and weaknesses?
Question 3: Are you comfortable with night shifts?
Answer:
I do believe in finding a work-life balance, therefore even if I’m available for any shift, I’d like to establish a regular routine so I can make other arrangements.
Read more at: Are you comfortable with night shifts?
Question 4: Why TCS?
Answer:
I need to develop the necessary skills to enter this competitive environment as a fresher. I determined that TCS was the ideal option because of its well-regarded training program, which will allow me to improve my abilities as necessary.
Question 5: Are you ready to work under a bond of 2 years?
Answer:
Yes, why not. My dream company is TCS. Joining such a huge company will make me pleased.
Read more at: Are you ready to work under a bond of 2 years?
Question 6: Who is the chairman of TCS?
Answer:
Natarajan Chandrasekaran
Question 7: Can you work under pressure?
Answer:
It will be easier for me to work under pressure if you are willing to improve on what you’re doing, and it will also assist me to produce work consistently.
Read more at: Can you work under pressure?
Question 8: When was TCS founded?
Answer:
1968.
Question 9: How would you rate me on a scale of 0-10 as an Interviewer?
Answer:
Sir, I don’t think I am in a position to analyze your interviewing approach, but if I had to, I would give it a rating. You get a 9 out of 10, as nobody on earth is perfect.
Read more at: How would you rate me on a scale of 0-10 as an Interviewer?
Question 10: Any questions?
Also Check:

 Apply For Jobs
Apply For Jobs Get Hiring Updates
Get Hiring Updates