What is Database Management System?
DBMS
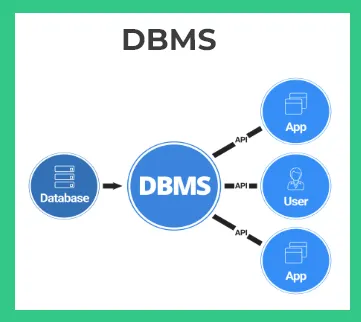
On this page, we will learn about what is database management system.A database management system (DBMS) is a software program that interacts with end-users, applications, and the database itself to capture and analyze the data. It is used to manage and organize large collections of data, such as financial records, customer information, and inventory records.
What is Database Management System?
The database management system is software that controls all the different manipulation of stored or to be stored data in a database. It allows the creation, update, manipulation, definition of a database.
As clear from the name it manages the whole database end to end for whatever operation that may be required. Some examples of DBMS are –
- SQL
- mySQL
- noSQL
- Oracle
- IBM DB2
- PostgreSQL
- MongoDB
A database management system perform the following –
- Database Definition
- Data Updation
- Data Retrieval
- Administration
- Security
Database Definition
This essentially defines how data is defined in the database. For example we have to create a database for students are PrepInsta users.
We will define the data as follows –
- Unique ID of signed up user
- Unique email ID of signed up user
- First Name
- Last Name
- Passwords etc
Data Updation
This majorly allows various operations like insertion of the new data, updating new data, deletion of data in the various database tables.
- Insertion – Inserting information of new user signed up on PrepInsta website
- Updation – Updating the password of the user who requested to change it
- Deletion – Deleting the complete or partial data of the user who has requested account deletion on PrepInsta.
Data Retrieval
The data is stored in various database servers and stored globally. For different instances like requesting login authentication details for a website. You need to communicate and retrieve a lot of data from database tables.
Administration
Database administration is important, a for a new employee who is working on database system for your company. You don’t want to give him deleting capabilities. So you create different roles like –
- Database Administrator – Who call perform all actions like modification, deletion, updation and creation etc.
- Database Manager – Who can define, update, modify but can’t delete
- Database Editor – Who can just retrieve and insert in the database
Note – The above are just for examples. Companies create their custom roles based upon exact requirements.
Security
The security of the system is also important. You don’t want hackers to steal your confidential database or maybe update your database with false data. Thus for any access to database node. There is an authentication that happens along.
Prime Course Trailer
Related Banners
Get PrepInsta Prime & get Access to all 200+ courses offered by PrepInsta in One Subscription
Get over 200+ course One Subscription
Courses like AI/ML, Cloud Computing, Ethical Hacking, C, C++, Java, Python, DSA (All Languages), Competitive Coding (All Languages), TCS, Infosys, Wipro, Amazon, DBMS, SQL and others




Login/Signup to comment