How to become a Cyber Security Expert in 2023?
Cyber Security Roadmap
Cyber Security is one of the demanding skills now-a-days. Here on this page we have discussed about How to become a Cyber Security Expert in 2023: Complete Roadmap, Step by step guide, skills required, and much more.
Table of Content:
- Introduction to Cyber security
- What is Cyber Security?
- Why Cyber Security ?
- Complete Roadmap for Cyber Security.
- Skills required to become a Cyber Security Expert.

Introduction
Cybersecurity, also known as computer security and information technology security, It is used to protect data, computers, electronic devices, servers, networks, and against malicious attacks. Cybersecurity is a broad term that can be applied in a variety of contexts, and the field can be divided into different categories:
- Network security
- Information security
- Application security
- Operational security
- Disaster recovery/business continuity planning
- Cloud security
- End-user education
- Critical infrastructure security
- Mobile security
- Software supply chain security
What is Cyber Security?
Cybersecurity refers to the practice of protecting computer systems, networks, and data fromunauthorized access, theft, damage, and disruption. It involves implementing measures and adopting strategies to safeguard information technology (IT) infrastructure, including computers, servers, mobile devices, and electronic systems, from various threats and attacks.
The primary objective of cybersecurity is to ensure the confidentiality, integrity, and availability of data and resources. Here are some key aspects of cybersecurity:
- Confidentiality: Protecting sensitive and confidential information from unauthorized access or disclosure. This involves measures such as encryption, access controls, and secure data storage.
- Integrity: Ensuring the accuracy, completeness, and reliability of data and systems. This includes preventing unauthorized modifications, data tampering, or unauthorized changes to configurations.
- Availability: Ensuring that computer systems, networks, and data are accessible and usable when needed. This involves implementing measures to prevent service disruptions, system failures, or denial-of-service attacks.
- Authentication and Authorization: Verifying the identity of users and granting appropriate access privileges. This includes the use of strong passwords, multi-factor authentication, and access control policies.
Why Cyber Security?
Cybersecurity is a complex and ever-evolving field due to continually emerging threats and the rapid advancement of technology. It requires a combination of technical expertise, proactive risk management, and a comprehensive approach to protect systems and data from potential cyber threats.
It is important to protect sensitive information, prevent financial loss, safeguard critical infrastructure, preserve privacy, maintain trust and reputation, and defend against evolving cyber threats. It is an essential component of the digital landscape and requires skilled professionals to ensure a secure and resilient environment.
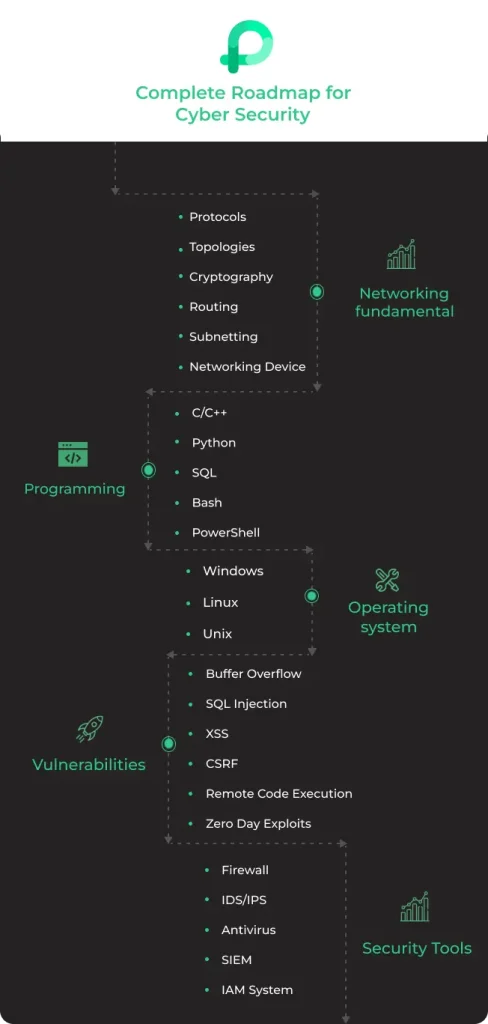
Skills required to become a Cyber Security Expert in just 12 Weeks !!
- Networking and Fundamentals
- Programming
- Operating System
- Vulnerabilities
- Security Tools
Check below to find a complete Roadmap and steps to become a Cyber Security Expert:
Roadmap to Cyber Security Expert
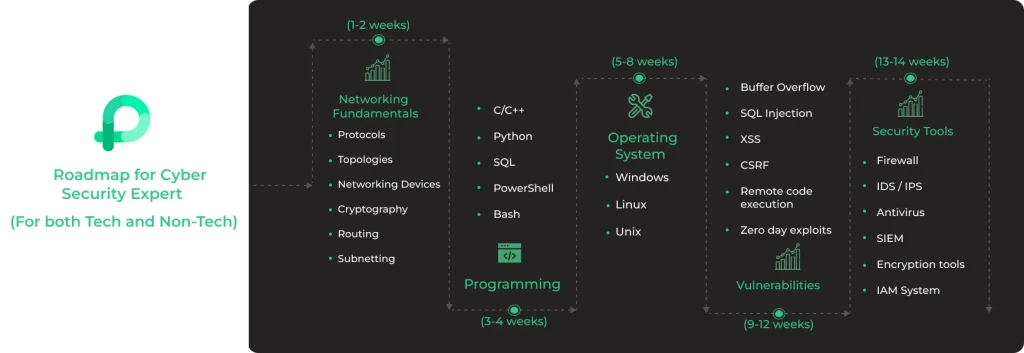
5 Steps to Become a Cyber Security Expert in 2023
Networking Fundamentals:
This is the first step towards becoming a cyber security expert. Networking fundamentals form the basis of communication between devices and systems in a networked environment. These fundamentals will form the basis for further study.
Programming:
You need to use the programming languages that are commonly used in cybersecurity, such as Python, Java, or C++. Understand secure coding practises and techniques to identify and mitigate common vulnerabilities. Familiarise yourself with scripting languages for automating security tasks.
Operating Systems:
This is a very important step on the roadmap. Try to gain proficiency in at least one major operating system like Windows, Linux, or Unix. Learn about secure configuration, user management, and access control mechanisms. Develop knowledge of system logs, auditing, and event monitoring.
Vulnerabilities:
Vulnerabilities in cybersecurity refer to weaknesses or flaws in software, systems, or processes that can be exploited by malicious actors to compromise the security and integrity of information or systems. Understanding vulnerabilities is crucial for cybersecurity professionals to identify and address potential risks.
Security Tools:
Security tools play a vital role in the field of cybersecurity by helping organizations detect, prevent, and respond to potential threats and vulnerabilities. These tools provide various functionalities and capabilities to enhance the security posture of systems and networks.
To know more about Cyber Security Expert Roadmap visit PrepInsta Prime
FAQ for How to become a Cyber Security Expert 2023
Essential skills for a career in cybersecurity include knowledge of networking concepts, operating systems, programming languages, encryption, vulnerability assessment, penetration testing, incident response, and security frameworks and standards.
Starting a career in cybersecurity typically involves gaining a strong foundation in computer science or a related field. Followed by high level cyber security certifications will also help boost your knowledge and skills.
While a degree in computer science, cybersecurity, or a related field can provide a solid foundation, it is not always mandatory. Many cybersecurity professionals enter the field through certifications, bootcamps, or self-study, combined with practical experience and continuous learning.
Cybersecurity offers various career paths, including roles such as cybersecurity analyst, network security engineer, penetration tester, security consultant, incident responder, security architect, and cybersecurity manager. Each path focuses on different aspects of cybersecurity, ranging from preventive measures to incident response and governance.
Click here to know about: Ethical Hacking
Get over 200+ course One Subscription
Courses like AI/ML, Cloud Computing, Ethical Hacking, C, C++, Java, Python, DSA (All Languages), Competitive Coding (All Languages), TCS, Infosys, Wipro, Amazon, DBMS, SQL and others



Login/Signup to comment